Smart Sensors and IoT: Security Best Practices
- BlogSmarter AI
- Edited by Ruth Kearney
- Blog
- April 19, 2026
- Updated:
Table of contents Show Hide
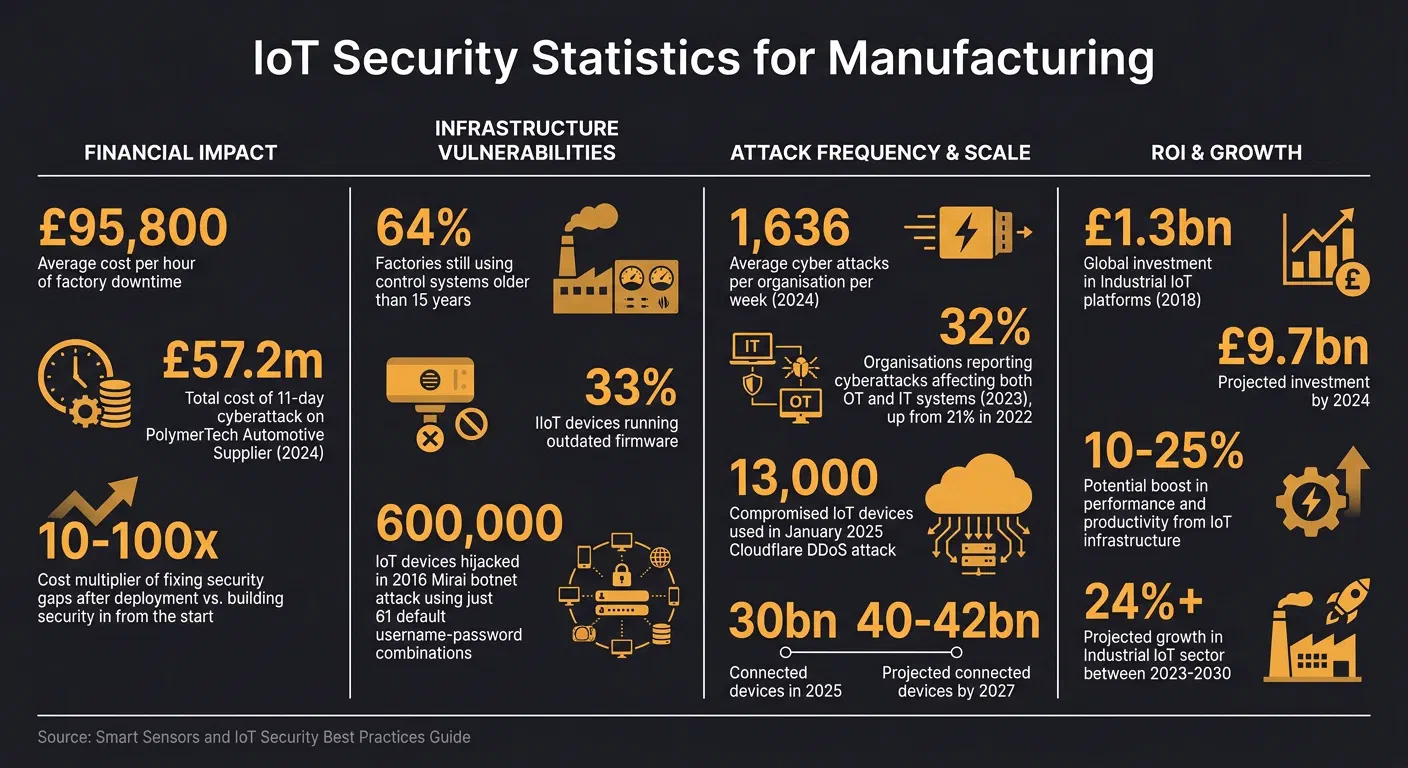
Insecure smart sensors stall production and burn margins fast. In 2023, 32% of organisations reported cyberattacks that hit both Operational Technology (OT) and Information Technology (IT) systems [1].
The problem is outdated systems. Many plants still run legacy control systems. Unpatched devices in your Internet of Things (IoT) estate create easy entry points for attackers.
Here’s the fix. This guide gives you practical steps for Industrial Internet of Things (IIoT) security. You’ll lock down weak spots, enforce strong authentication, encrypt data, and respond before issues snowball.
What you’ll get:
- Secure hardware tips: Stop relying on default credentials and use tamper-resistant components.
- Software safeguards: Implement cryptographic signing and encrypted updates to keep attackers out.
- Authentication upgrades: Use multi-factor authentication and role-based access control to tighten security.
- Real-time monitoring: Spot anomalies before they disrupt your operations.
Industrial IoT Security Essentials (Key Risks and How to Mitigate Them)
Security Principles for Smart Sensor Design
IoT breaches often stem from devices lacking built-in security from the outset. Fixing these gaps later can cost 10 to 100 times more, and in many cases, hardware recalls are the only option. The 2016 Mirai botnet attack highlighted this issue, hijacking around 600,000 IoT devices using just 61 default username-password combinations[6]. As Hubble Network put it:
“The vulnerability wasn’t introduced when those devices connected to the internet. It was integrated during manufacturing”[6].
To avoid such disasters, security must be baked into both hardware and software before production begins. This is especially critical in manufacturing, where sensors are expected to work reliably for 5 to 15 years[6]. Spotting a major flaw years into deployment? That’s a nightmare no one can afford.
Secure Hardware Selection
The foundation of secure sensor design is choosing tamper-resistant hardware. Start with a hardware root of trust - components like Trusted Platform Modules (TPMs), Secure Elements, or Physically Unclonable Functions (PUFs). These provide a unique identity for each device and form the bedrock for all other security measures. Without this, your security efforts are built on shaky ground[6].
Another essential layer is secure boot. During startup, the bootloader verifies cryptographic signatures of firmware stages against keys stored in the root of trust. This ensures only authorised code runs. Disable development ports like Joint Test Action Group (JTAG) and Universal Asynchronous Receiver-Transmitter (UART) before deployment to prevent unauthorised access. For sensors in exposed environments, active mesh layers detect tampering and wipe memory to protect sensitive data.
Adding a crypto authentication IC, such as the Microchip ATECC608 or Infineon OPTIGA Trust, strengthens security further. These chips handle cryptography and key storage for less than £0.40 per unit in large-scale production[6]. Selecting microcontrollers with built-in secure elements during the design phase avoids costly retrofits later.
Default credentials? Bin them. Instead, inject unique X.509 certificates or device-specific keys during a factory “key injection ceremony” using a Hardware Security Module (HSM). This ensures that compromising one device doesn’t compromise the entire fleet. Zero-touch provisioning also helps by allowing devices to present hardware-backed identities to cloud systems without manual setup, reducing errors and speeding up deployment.
Hardware security alone isn’t enough. Without secure software, even the best hardware leaves you exposed.
Secure Software Development
The software running on your sensors must be as secure as the hardware. Start with secure coding practices and maintain a Software Bill of Materials (SBOM) - a detailed inventory of all software components and libraries. This makes it easier to identify and patch vulnerabilities when new Common Vulnerabilities and Exposures (CVEs) are announced.
Code signing is non-negotiable. Every firmware image should be cryptographically signed using keys stored in a Hardware Security Module. Devices must verify these signatures before installing updates, preventing attackers from sneaking in malicious firmware. Pair this with encrypted Over-the-Air (OTA) updates and automatic rollback features to ensure failed updates don’t leave devices bricked.
Follow the principle of least privilege. Limit what each software component can access to contain breaches and stop attackers from taking full control of the system. Isolate new sensors in a Virtual Local Area Network (VLAN) until they pass firmware and certificate validation checks. This quarantine approach stops compromised devices from spreading malware across your network.
Have a vulnerability disclosure policy in place, aligned with standards like ISO 29147. Make it easy for researchers and users to report security flaws, and commit to fixing them within a set timeframe. The National Cyber Security Centre advises:
“It’s important that organisations understand whether you have processes in place to ensure that cyber security is considered from the design phase, through development, and into long term support”[7].
Finally, scrutinise your supply chain. Insist on provenance documentation for microcontrollers and secure elements to avoid counterfeit parts with backdoors. Check that contract manufacturers have both physical controls (like restricted access to programming stations) and logical protections (such as network segmentation). A weak link in your supply chain can undo all your hard work.
Authentication, Authorisation, and Identity Management
Once your hardware and software are locked down, the next step is controlling who and what can access your sensors. In manufacturing, where sensors might run for years without direct human oversight, weak authentication can leave systems wide open. As eMudhra points out:
“Authentication controls access to manufacturing devices and systems” [9].
A stark reminder of the risks came in January 2025, when Cloudflare blocked a massive DDoS attack driven by a Mirai-botnet variant. This attack used 13,000 compromised IoT devices, including routers and cameras [5]. With 30 billion connected devices in 2025 - and projections hitting 40–42 billion by 2027 [5] - any sensor without proper authentication becomes a potential weak spot.
The Role of Public Key Infrastructure (PKI)
For manufacturing IoT, Public Key Infrastructure (PKI) with digital certificates sets the standard. Every device gets a unique X.509 certificate signed by a trusted Certificate Authority (CA), ensuring its identity. Pair this with Mutual TLS (mTLS) - where both the device and the server authenticate each other - and you’ve got a solid base for secure communication.
To go further, cryptographic keys should be stored in hardware-backed components like Trusted Platform Modules (TPMs) or Secure Elements (SEs). This prevents attackers from extracting keys through software-based methods.
Avoid pre-shared keys (PSK) for large-scale deployments. They’re risky and hard to manage — one compromised key can jeopardise the entire system. Instead, token-based authentication, such as JSON Web Token (JWT) or OAuth 2.0, works better for API access, provided you have secure, centralised management in place.
Multi-Factor Authentication for IoT Systems
Passwords alone just don’t cut it anymore. The Information Commissioner’s Office puts it bluntly:
“Using a password only, even a strong one, may not provide sufficient security against more sophisticated attacks” [12].
Multi-factor authentication (MFA) is the answer. It combines multiple verification factors: something you know (password), something you have (hardware token), and something you are (biometrics). For example, pairing a password with a biometric scan or a hardware token adds critical layers of defence.
For devices, hardware-backed authentication using TPMs or SEs raises the bar even higher. An attacker would need both physical access to the device and the securely stored cryptographic key to break in.
The UK’s Product Security and Telecommunications Infrastructure (PSTI) Regulations 2024 also raise the stakes. They demand unique passwords for each product or user-defined ones, alongside a public vulnerability disclosure policy [12].
Automating certificate lifecycle management - handling provisioning, renewal, and revocation across large device fleets - helps eliminate gaps caused by expired credentials. This not only reduces manual work but also strengthens your overall security posture.
Role-Based Access Control (RBAC)
While authentication checks who someone is, authorisation controls what they can do. Role-Based Access Control (RBAC) enforces the Principle of Least Privilege, granting only the permissions needed for a specific role. For example, roles like “Maintenance Technician” or “Plant Manager” can group permissions to simplify access control [10].
In Industry 4.0 setups, RBAC is crucial. It prevents unauthorised users from issuing harmful commands to critical machinery, like robotic arms or CNC machines [8]. A maintenance technician might only have “read” and “RPC call” rights for certain sensors, while a plant manager could oversee operations but wouldn’t be allowed to push firmware updates.
RBAC also helps with multi-tenant isolation. Contractors or external teams can be limited to accessing only the data and devices they’re authorised to work on. This reduces risks like industrial espionage or accidental data leaks [10].
Adding an API Gateway between user applications and the IoT data plane adds another layer of protection. It ensures that Message Queuing Telemetry Transport (MQTT) topics aren’t directly exposed, enforcing RBAC policies more effectively [11]. Regularly auditing device policies with automated tools is also key — this helps spot expiring certificates or over-permissive roles before they become a problem.
Encryption and Communication Protocols for Data in Transit
Once you’ve nailed down who gets access to your sensors with solid authentication, the next step is protecting the data while it’s on the move. In manufacturing, this means safeguarding everything from mill certificate readings to furnace temperature metrics and production counts. Without encryption, this data is wide open to interception or tampering by anyone with access to the network. Andrej Kovacevic puts it bluntly:
“Data in transit is effectively a cash-in-transit van; it is never more vulnerable than when it is moving” [18].
The go-to method for securing IoT data streams is Transport Layer Security (TLS), which ensures that intercepted packets are useless to prying eyes [16]. For devices using UDP - think real-time sensor streams running on the Constrained Application Protocol (CoAP) - Datagram Transport Layer Security (DTLS) 1.2 has you covered [13].
TLS and Secure Communication Channels
TLS 1.3 is the top pick for IoT devices that need to conserve bandwidth and battery life. It trims the handshake process to just one Round Trip Time (RTT) compared to the two RTTs required by TLS 1.2 [15]. It also enforces forward secrecy, so even if a device’s private key is compromised later, past sessions stay secure. In manufacturing, Mutual TLS (mTLS) is the gold standard. Both the device and the broker must present X.509 certificates to authenticate themselves before exchanging data [15].
When setting up MQTT, always route encrypted traffic through port 8883 (MQTTS) [17]. Devices with hardware AES acceleration, like the ESP32, work best with the cipher suite TLS_AES_128_GCM_SHA256. This suite combines confidentiality and integrity into one efficient operation. Meanwhile, make sure to disable outdated protocols like SSLv3, TLS 1.0, and TLS 1.1 - they’re riddled with vulnerabilities like POODLE [17].
For device certificates, switching from RSA-2048 to ECDSA P-256 shrinks the key size from 256 bytes to just 32, speeding up handshakes on low-power devices [15]. Store private keys in a Secure Element (SE) or Hardware Security Module (HSM) to keep them safe, even if your device firmware is compromised. Always validate X.509 certificate chains against a trusted Root CA, and steer clear of any settings that allow skipping validation [14] [16]. Once secure channels are in place, ensuring data integrity becomes the next priority.
Data Integrity with Message Authentication Codes
Encryption isn’t the whole story. You also need to confirm the data hasn’t been tampered with during transit. Message Authentication Codes (MACs) or Authenticated Encryption with Associated Data (AEAD) tags on each record flag any unauthorised changes [13]. In DTLS, a MAC is generated using a 64-bit value that combines an epoch field and a sequence number, effectively preventing replay attacks [13].
For devices with tight resource constraints, TLS-PSK (Pre-Shared Key) cipher suites can sidestep the heavy lifting of public-key operations [17]. However, this approach comes with risks: compromise one key, and your whole system could be at stake. A better option for large-scale setups is certificate pinning. This ensures devices connect only to specific endpoints, even if those endpoints have a valid CA signature [14].
To save bandwidth on frequent, small messages, session resumption is a game-changer. By using Session IDs or Session Tickets, devices can skip the full handshake when reconnecting, keeping overheads low [17]. This is especially useful for sensors that need to send constant updates without wasting resources on repetitive handshakes.
Continuous Monitoring and Threat Detection
Having solid hardware and software security is just the start. Continuous monitoring steps up to handle the ever-changing threat landscape. Real-time monitoring is what catches anomalies before they snowball into major breaches or system shutdowns. And the stakes are high — organisations face an average of 1,636 cyber attacks every week[20]. In manufacturing, where IT and OT systems are more intertwined than ever, even one compromised sensor could lead attackers straight to your Supervisory Control and Data Acquisition (SCADA) or Programmable Logic Controller (PLC) systems. Without constant vigilance, problems can lurk unnoticed until something breaks.
Real-Time Threat Detection
Spotting anomalies is your frontline defence. It starts by learning what “normal” looks like for each device - things like typical traffic levels, reset patterns, or operating temperatures. Any deviation from this baseline triggers an alert. As Chris Coleman, CTO at Memfault, points out:
“Looking for anomalies in device behaviour is one of the easiest ways to detect a security problem - and one of the most overlooked”[19].
For instance, a temperature sensor suddenly sending gigabytes instead of kilobytes? That’s a massive red flag. Same goes for a device rebooting out of the blue or connecting to an unknown IP address.
In manufacturing, Isolation Forest algorithms are a game-changer. They’re quick, handle numerical sensor data with ease, and don’t need pre-labelled training sets[21]. These algorithms excel at pinpointing unusual data points, triggering real-time alerts on the shop floor. Combine this with network traffic monitoring - tracking both incoming and outgoing flows - and you can catch threats like unauthorised access, cryptojacking (which can drive up power usage by 15–25%[22]), or botnet activity before they spiral out of control.
But spotting the problem is just the beginning. The real challenge lies in how you respond.
Incident Response Planning
Detection without action is useless. Every alert should automatically kick off a clear, predefined response. Set up a tiered alert system to avoid drowning in notifications:
- Informational: Log only - no immediate action required.
- Warning: Needs attention within the shift.
- Critical: Requires an immediate response[23].
Make sure alerts are routed to the right people - machine faults to operators, vibration anomalies to maintenance, and network issues to IT. Each alert type should have a detailed runbook outlining what it means, who’s responsible, and the exact steps to troubleshoot. For example, if a gateway’s heartbeat signal is missed, the runbook should specify whether to check the network first or escalate to IT immediately. After resolving any issue, conduct a root cause analysis to close the loophole for good[1]. As François Baldassari, CEO of Memfault, advises:
“Building this muscle now will position your team to better navigate future regulatory requirements”[19].
Don’t stop at alerts and responses - network segmentation is crucial. Breaking your network into smaller segments or micro-segments can stop malware from spreading across critical systems[1][2]. Adding an Industrial Demilitarised Zone (IDMZ) between IT and OT networks gives you an extra layer of protection. If one side gets hit, the other stays safe[1].
Compliance and Industry Standards for IoT Security
Regulations aren’t just about avoiding fines - they’re about protecting your business and earning customer trust. In the UK, manufacturers must meet the requirements of the PSTI Act, UK GDPR, and the Data (Use and Access) Act, which takes effect on 19 June 2025 [24]. These regulations set the baseline for securing devices and handling personal data. Falling short could mean hefty fines or damage to your reputation. For IoT devices, compliance goes hand in hand with solid design and constant monitoring to keep vulnerabilities at bay.
Key IoT Security Standards
For consumer IoT devices, the PSTI Act and ETSI EN 303 645 set the rules. The PSTI Act outlaws default passwords, requires clear communication about support periods, and insists on a process for reporting vulnerabilities [7]. ETSI EN 303 645 serves as the UK and European benchmark for consumer IoT security, outlining 13 key provisions such as secure software updates and vulnerability disclosure [7][24].
Industrial IoT deployments have their own playbook. Standards like IEC 62443 and ISO/IEC 27001 focus on strict security controls for industrial environments. The NCSC’s 11 Device Security Principles offer practical advice for ensuring device integrity, securing updates, and safeguarding data in storage and transit [7]. For handling vulnerabilities, ISO/IEC 29147 and ISO/IEC 30111 are the go-to international standards. Across the pond, NIST IR 8259A provides a detailed list of cybersecurity requirements for IoT devices, which many manufacturers adopt globally [7]. When documenting security measures, stick to clear language: use ‘Shall’ for must-haves, ‘Should’ for recommended practices, and ‘Can’ for optional improvements [7].
Beyond technical security, manufacturers also need to meet obligations around sustainability and traceability.
Meeting Sustainability and Traceability Requirements
IoT systems aren’t just about security - they’re also key to meeting sustainability goals. For example, if you’re tracking waste or monitoring emissions using tools like the Microsoft Emissions Impact Dashboard under the ISO 14000 series, your sensors must provide accurate, tamper-proof data [25][4]. Rochelle Samuel from Saint Gobain highlighted the industry’s focus on Scope 3 CO₂ emissions at a recent event, saying:
“I especially gained value from the Executive Micro-Summit, where I networked with other sustainability leaders in the industry to discuss opportunities and challenges related to scope 3 CO₂ emissions” [4].
For metals manufacturers, secure IoT systems enable Digital Lean practices, helping you cut waste and optimise production with real-time data [4]. Aligning your data flow with ANSI/ISA-95 for control integration doesn’t just tick compliance boxes - it helps you make faster production decisions. With global investment in Industrial IoT platforms expected to jump from £1.3 billion in 2018 to £9.7 billion by 2024, IoT infrastructure could boost your performance and productivity by 10% to 25% [26].
Conclusion
Securing IoT devices isn’t a box-ticking exercise. It’s what keeps your production lines moving and your business out of the red. In 2023, 32% of organisations reported cyberattacks affecting both OT and IT systems, a jump from 21% in 2022 [1]. With billions of connected devices out there, each vulnerability is an open door waiting to be exploited.
But here’s the good news: you don’t need to rip everything apart to get it right. Start with the basics. Update default credentials, keep critical networks isolated, and use real-time monitoring to spot issues before they snowball [1][3]. As Dawn Illing from GlobalSign points out:
“Security-by-design is paramount, it begins at the point of manufacture, which then allows organisations to provide critical security updates remotely, automatically, and from a position of control” [30].
With the Industrial IoT sector projected to grow by more than 24% between 2023 and 2030 [26], securing your IoT infrastructure isn’t just about avoiding downtime — it’s about staying ahead. By combining secure design, strong authentication, and proactive monitoring, you can turn your connected devices into a real advantage. Start with one line or product family, secure the certificate flow, then expand across operations.
FAQs
What’s the quickest way to eliminate default credentials across my sensor fleet?
How do I roll out mTLS certificates to thousands of devices without manual effort?
What should I monitor to spot an IoT breach before it causes downtime?
About the Author

Editor · Co-Founder & CEO
Ruth Kearney is Co-Founder and CEO of GoSmarter AI — driving commercial growth and strategic partnerships to help metals manufacturers adopt AI and digital tools that actually deliver on the shop floor.